how I can solve Task 2.1A ( Q!, Q2, and Q3) ? ...
![3. Task Set 2: Writing Programs to Sniff and Spoof Packets Task 2.1: Writing Packet Sniffing Program Sniffer programs can be easily written using the pcap library. With pcap, the task of sniffers becomes invoking a simple sequence of procedures in the pcap library. At the end of the sequence, packets will be put in buffer for further processing as soon as they are captured. All the details of packet capturing are handled by the pcap library The SEED book Computer Security: A Hands-on Approach provides a sample code in Chapter 12, showing how to write a simple sniffer program using pcap. We include the sample code in the following (see the book for detailed explanation) t include <pcap.h> #include <stdio.h> This function will be invoked by pcap for each captured packet We can process each packet inside the function void got_packet(u_char args, const struct pcap_pkthdr *header, const u_char packet) printf(Got a packet ); int main() This project is based on SEED labs by Wenliang Du, Syracuse University pcap_t *handle; char errbuf[PCAP_ERRBUF_SIZE]; struct bpf_program fp; char filter_exp[]-ip proto icmp; bpf_u_int32 net; // Step 1: Open live pcap session on NIC with name eth3 // Students needs to change eth3 to the name // found on their own machines (using ifconfig) handle = pcap-open-live ( eth3, BUFSIZ, 1, 1000, errbuf); // Step 2: Compile filter_exp into BPF psuedo-code pcap compile(handle, &fp, filter_exp, e, net) pcap_setfilter(handle, &fp); // Step 3: Capture packets pcap_loop (handle, -1, got_packet, NULL); pcap_close (handle); //Close the handle return 0; // Note: dont forget to add-1pcap to the compilation command. // For example: gcc -o sniff sniff.c -1pcap Tim Carstens has also written a tutorial on how to use pcap library to write a sniffer program The tutorial is available at http://www.tcpdump.org/pcap.htm.](https://www.subjectmate.com/img/openquestion/401uid1598813131mceclip0.png)
how I can solve Task 2.1A ( Q!, Q2, and Q3) ?
and 2,1 B , what is the code ?
and how I can sniff password ?
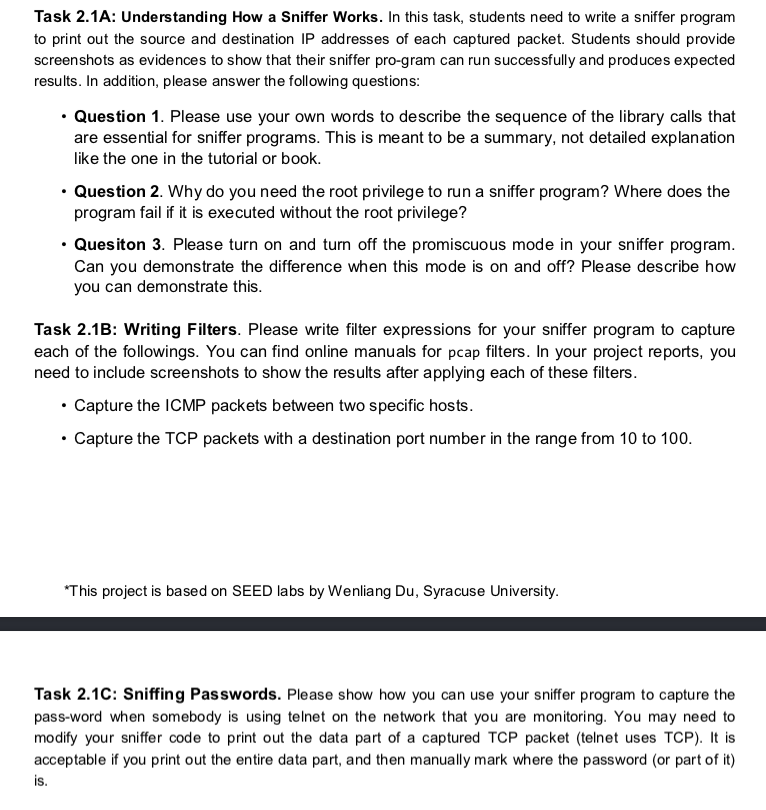
3. Task Set 2: Writing Programs to Sniff and Spoof Packets Task 2.1: Writing Packet Sniffing Program Sniffer programs can be easily written using the pcap library. With pcap, the task of sniffers becomes invoking a simple sequence of procedures in the pcap library. At the end of the sequence, packets will be put in buffer for further processing as soon as they are captured. All the details of packet capturing are handled by the pcap library The SEED book "Computer Security: A Hands-on Approach" provides a sample code in Chapter 12, showing how to write a simple sniffer program using pcap. We include the sample code in the following (see the book for detailed explanation) t include <pcap.h> #include <stdio.h> This function will be invoked by pcap for each captured packet We can process each packet inside the function void got_packet(u_char args, const struct pcap_pkthdr *header, const u_char "packet) printf("Got a packet\n"); int main() This project is based on SEED labs by Wenliang Du, Syracuse University pcap_t *handle; char errbuf[PCAP_ERRBUF_SIZE]; struct bpf_program fp; char filter_exp[]-"ip proto icmp"; bpf_u_int32 net; // Step 1: Open live pcap session on NIC with name eth3 // Students needs to change "eth3" to the name // found on their own machines (using ifconfig) handle = pcap-open-live ( "eth3", BUFSIZ, 1, 1000, errbuf); // Step 2: Compile filter_exp into BPF psuedo-code pcap compile(handle, &fp, filter_exp, e, net) pcap_setfilter(handle, &fp); // Step 3: Capture packets pcap_loop (handle, -1, got_packet, NULL); pcap_close (handle); //Close the handle return 0; // Note: don't forget to add"-1pcap" to the compilation command. // For example: gcc -o sniff sniff.c -1pcap Tim Carstens has also written a tutorial on how to use pcap library to write a sniffer program The tutorial is available at http://www.tcpdump.org/pcap.htm.
Task 2.1A: Understanding How a Sniffer Works. In this task, students need to write a sniffer program to print out the source and destination IP addresses of each captured packet. Students should provide screenshots as evidences to show that their sniffer pro-gram can run successfully and produces expected results. In addition, please answer the following questions: Question 1. Please use your own words to describe the sequence of the library calls that are essential for sniffer programs. This is meant to be a summary, not detailed explanation like the one in the tutorial or book. Question 2. Why do you need the root privilege to run a sniffer program? Where does the program fail if it is executed without the root privilege? Quesiton 3. Please turn on and turn off the promiscuous mode in your sniffer program. Can you demonstrate the difference when this mode is on and off? Please describe how you can demonstrate this Task 2.1B: Writing Filters. Please write filter expressions for your sniffer program to capture each of the followings. You can find online manuals for pcap filters. In your project reports, you need to include screenshots to show the results after applying each of these filters. Capture the ICMP packets between two specific hosts. Capture the TCP packets with a destination port number in the range from 10 to 100. This project is based on SEED labs by Wenliang Du, Syracuse University. Task 2.1C: Sniffing Passwords. Please show how you can use your sniffer program to capture the pass-word when somebody is using telnet on the network that you are monitoring. You may need to modify your sniffer code to print out the data part of a captured TCP packet (telnet uses TCP). I is acceptable if you print out the entire data part, and then manually mark where the password (or part of it) is
Solved
COMPUTER SCIENCE
1 Answer
Pushpa babu
Login to view answer.